AZ-140 Note #2 Implement an Azure Virtual Desktop infrastructure
Plan to Implement Remote Desktop Protocol Shortpath
Connection Options:
• Point-to-Site VPN: Secure, encrypted connection between a single device and a virtual network. Ideal for developers or small-scale setups.
• Site-to-Site VPN: Secure connection between on-premises resources and Azure using a VPN Gateway.
• Azure ExpressRoute: Private, dedicated connection to Azure, bypassing the internet.
Traffic Filtering:
• Network Security Groups (NSGs): Control inbound and outbound traffic between resources by IP, port, and protocol.
• Network Virtual Appliances (NVAs): Use VMs to perform network functions like firewalls or WAN optimization.
Traffic Routing:
• Route Tables: Create custom routes to control traffic within subnets.
• BGP Routes: Propagate on-premises BGP routes to Azure using a VPN or ExpressRoute.
Service Integration:
• Private Access: Deploy Azure services directly into a virtual network for private access.
• Private Link: Secure, private access to specific services within the network.
• Service Endpoints: Extend a virtual network to secure service resources.
Analyzing Connection Quality in Azure Virtual Desktop
Azure Virtual Desktop (AVD) provides a seamless remote experience by hosting client sessions on Azure-based session hosts. Ensuring high connection quality is crucial for user experience, and this can be analyzed using Azure Log Analytics.
Connection Data Analysis
1. Network Data (NetworkData Table)
• Measures bandwidth, round-trip time (RTT), and assigns a Correlation ID for tracking.
• Data is collected every two minutes during active sessions.
2. Graphics Data (ConnectionGraphicsData Table - Preview)
• Used when users report slow or choppy performance.
• Captures end-to-end delay, dropped frames, encoding/decoding delays, and bandwidth.
• Triggered only when issues occur (e.g., high frame drops or delays).
Key Metrics for Troubleshooting
• Round-trip time (RTT): Measures latency between user and session host.
• End-to-end delay: Includes encoding, network, and rendering delays.
• Dropped frames: Indicates network, client, or server issues.
Collection Frequency
• Network data: Every 2 minutes.
• Graphics data: Only when performance falls below thresholds.
This analysis helps administrators identify and resolve network or graphical bottlenecks, ensuring an optimal user experience in Azure Virtual Desktop.
RDP Bandwidth Requirements
Overview
Remote Desktop Protocol (RDP) dynamically optimizes graphics delivery based on computing resources and network conditions. It multiplexes multiple Dynamic Virtual Channels (DVCs) for graphics, input, device redirection, and more. Bandwidth usage varies based on user activity, application type, and display resolution.
Bandwidth Estimation
• Graphics & Input: Depends on user actions.
• File Transfers & Printing: Uses bulk compression (similar to .zip rates).
• Other Factors: Voice/video conferencing, 4K streaming, and real-time communication impact usage.
Graphics Bandwidth Usage (1920x1080 Resolution)
• Idle: ~0.3 Kbps
• Microsoft Office Apps: 100 Kbps – 500 Kbps
• Web Browsing: 6 Mbps (Default) / 1 Mbps (H.264)
• Image Gallery: 3.6 Mbps (Default) / 0.8 Mbps (H.264)
• Video Playback (30 FPS): 8.5 Mbps (Default) / 2.8 Mbps (H.264)
Dynamic Bandwidth Allocation
RDP adapts dynamically based on network conditions, adjusting image quality and frame rate to optimize performance.
Bandwidth Throttling (QoS Policy)
• Implement using Group Policy for domain-joined session hosts.
• Set an Outbound Throttle Rate for RDP traffic.
• Apply QoS settings to svchost.exe (port 3390, UDP protocol).
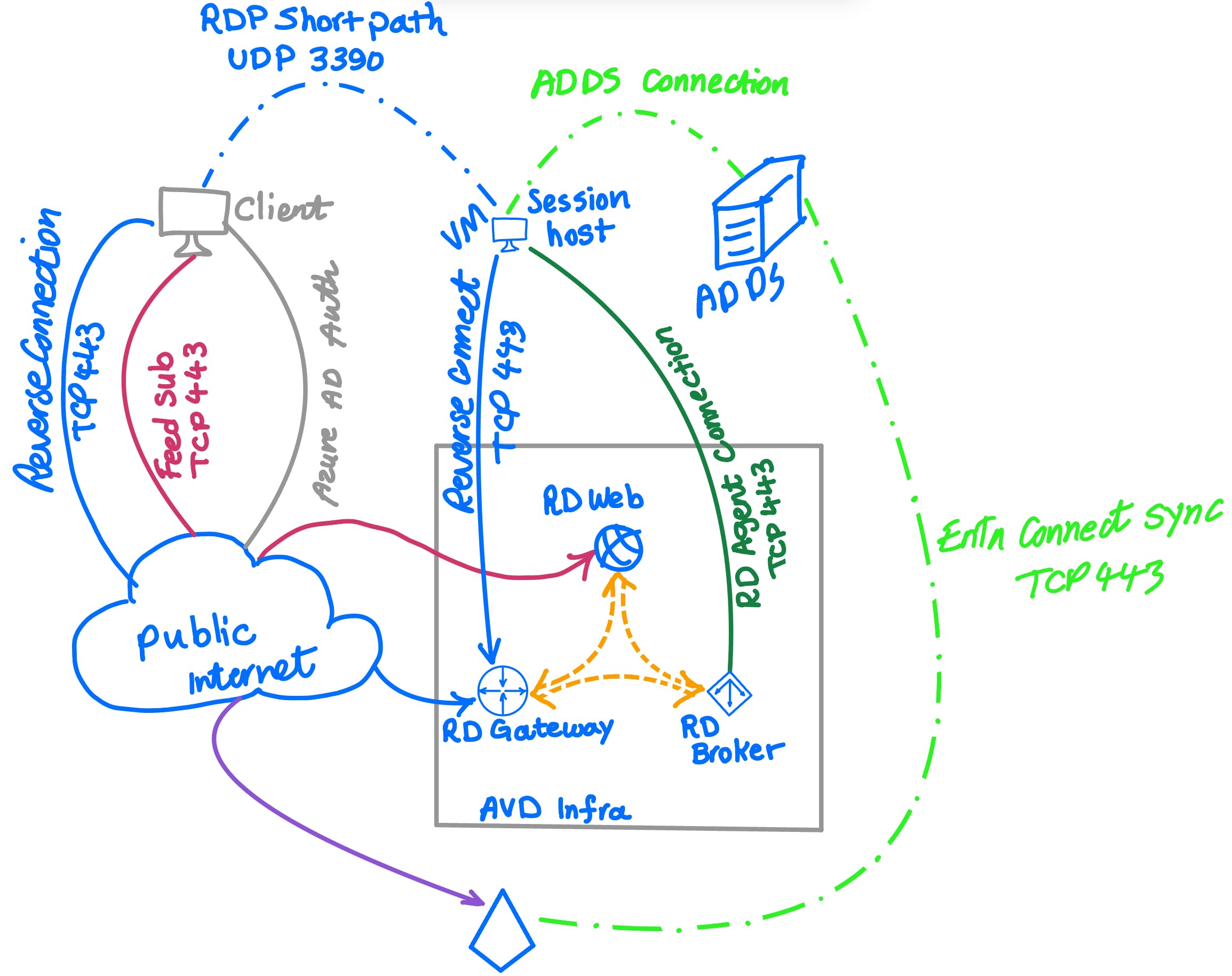
RDP Shortpath for Azure Virtual Desktop
Overview
RDP Shortpath enhances Azure Virtual Desktop (AVD) connections by enabling a direct UDP-based transport between the client and session host. (it overrides VPN Gateway if we use)This improves reliability and reduces latency compared to the default TCP-based reverse connect transport, which is used as a fallback for compatibility. So we are skipping the gateway..
How to check if its RDP Shortpath:
1. Check the RDP Client’s Connection Information
During an active session:
Press Ctrl + Alt + Home to open the RDP connection bar.
Click the connection information icon and select Show detail.
Look for the Transport Protocol field:
UDP: Connection is using RDP Shortpath.
TCP (or WebSocket): Fallback to traditional reverse connect transport.

2. Check Event Viewer Logs on the Session Host
Open Event Viewer (
eventvwr.msc).Navigate to:
Applications and Services Logs → Microsoft → Windows → TerminalServices-RDPClient/Operational.Look for Event ID 131 (UDP connection initiated) and Event ID 135 (UDP connection successful).
These confirm RDP Shortpath is active.
3. Use PowerShell to Check Listener Ports
On the session host, run:
powershell
Copy
Get-NetUDPEndpoint -LocalPort 3390- If UDP port
3390is listening, RDP Shortpath is enabled.
- If UDP port
4. Azure-Specific Verification
Test connectivity to the session host’s UDP port 3390:
powershell
Copy
Test-NetConnection -ComputerName <SessionHostIP> -Port 3390 -Udp- If the result shows UDP port 3390 is open, RDP Shortpath is reachable.
Check Azure Monitor (for Azure Virtual Desktop):
Navigate to the Host Pool → Diagnostics → Connections.
Filter for connection details showing
TransportProtocol: UDP.
5. Network Packet Capture (Advanced)
Use tools like Wireshark to monitor traffic:
Filter for
udp.port == 3390during an RDP session.If UDP packets are flowing, RDP Shortpath is active.
Connection Types
1. Managed Networks (Private VPNs, ExpressRoute)
• Establishes direct UDP connectivity via private connections.
• Requires enabling a UDP listener (default port: 3390).
• Supports QoS for prioritization and traffic throttling.
2. Public Networks (Internet-based connections)
• Uses STUN for direct UDP connections.
• Falls back to TURN (preview) when direct connectivity isn’t possible.
• Relies on ICE to optimize connection establishment.
Key Benefits
• Enhanced performance via Universal Rate Control Protocol (URCP).
• Lower latency due to fewer relay points.
• Improved reliability for latency-sensitive applications.
Connection Sequence
• Starts with TCP-based reverse connect transport.
• Attempts direct UDP connection via STUN.
• If STUN fails, TURN relays traffic through an intermediary.
• Establishes secure TLS-over-UDP for stable RDP transport.
Firewall & NAT Considerations
• UDP must be allowed for STUN-based direct connections.
• TURN helps in restrictive network environments.
• Default ephemeral UDP ports range 49152–65535 (except 65330).
RDP Shortpath for Azure Virtual Desktop: Connection Scenarios
These scenarios illustrate how connections are evaluated to determine if RDP Shortpath is used across different network topologies.
1. Public Network (STUN) – A UDP connection is established over the internet, with no VPN available. Firewall/NAT allows UDP traffic.
2. Public Network (TURN Relay) – Direct UDP is blocked, but an indirect UDP connection is relayed via TURN.
3. Public Network with VPN – Multiple routes exist, and the lowest-latency path (e.g., VPN) is chosen.
4. Managed & Public Networks Enabled – Connections are attempted simultaneously, with the first-found algorithm prioritizing the managed network due to fewer steps.
5. Forced Route Selection – Admin blocks a specific route (e.g., VPN UDP), ensuring ICE/STUN uses the remaining available path.
6. TURN Relay with Blocked VPN UDP – Both RDP Shortpath types are enabled, but UDP over VPN is blocked. TURN relays the connection over a public network.
7. Fallback to TCP – If UDP connections fail entirely, RDP Shortpath falls back to TCP-based reverse connect transport.
Managing Connectivity for On-Premises Networks
RDP Shortpath for Managed Networks provides direct UDP-based transport between Remote Desktop Clients and session hosts, enabling Quality of Service (QoS) policies for better performance.
Why QoS Matters
QoS prioritizes real-time RDP traffic over less critical data (e.g., app downloads), reducing:
• Jitter – Prevents visual and audio glitches.
• Packet Loss – Avoids retransmissions and delays.
• High Latency – Minimizes lag between input and response.
QoS Implementation
Instead of increasing bandwidth, QoS helps manage existing resources by:
1. Enabling RDP Shortpath for Managed Networks (QoS isn’t supported for reverse connect transport).
2. Inserting DSCP markers via Group Policy to classify and prioritize RDP packets.
3. Ensuring consistent QoS settings across all network devices.
Key Considerations
• VPNs add latency and limit QoS effectiveness outside managed networks.
• Global organizations benefit from QoS due to limited bandwidth on long-distance links.
• QoS-enabled routers prioritize RDP like a “carpool lane” for critical traffic.
Recommended DSCP Value: 46 (Expedited Forwarding - EF) to ensure high-priority delivery.
By aligning RDP and network configurations, QoS can eliminate delays, packet loss, and jitter, ensuring a smooth remote experience.
Plan and implement an Azure Private Link solution for Azure Virtual Desktop
Azure Private Link enhances security by enabling private connectivity between Azure Virtual Desktop (AVD) and your virtual network, keeping traffic within Microsoft’s network and eliminating exposure to the public internet. Users can connect via VPN or ExpressRoute for added security.
How Private Link Works in AVD
Private Link supports three key workflows, each requiring private endpoints:
1. Initial Feed Discovery – A single private endpoint for all workspaces, enabling users to discover their assigned workspaces.
2. Feed Download – A private endpoint per workspace to download connection details.
3. Host Pool Connections – A private endpoint per host pool for secure remote session connections.
Supported Scenarios
Private Link can be implemented in different ways depending on network requirements:
• Full Private Route: All AVD traffic (initial feed, feed download, remote sessions) uses private endpoints.
• Partial Private Route: Feed discovery remains public while feed download and remote sessions use private endpoints.
• Minimal Private Route: Only remote session traffic is private; other workflows use public routes.
• No Private Link: All traffic uses public routes.
Key Considerations
• Initial Feed Discovery must use a designated workspace, and deleting it will break feed discovery.
• The workspace for initial feed discovery is always accessible via public routes, even if configured for private access.
Implementing Private Link ensures a secure and controlled AVD deployment, reducing exposure to public networks while maintaining seamless user access.
Create an RDP Connection to a Windows VM Using Azure Bastion
Summary:
Azure Bastion allows secure, clientless RDP connections to Windows VMs in an Azure virtual network directly through the Azure portal. It eliminates the need to expose RDP/SSH ports to the internet while ensuring seamless access.
Prerequisites:
• Azure Bastion Host: Must be deployed in the VM’s virtual network. (See Create a Bastion Host for setup.)
• Windows Virtual Machine: Located in the same virtual network as Bastion.
• Required Roles:
• Reader role on VM, NIC (with private IP), Bastion resource, and virtual network (if peered).
Ports Required:
• RDP (3389) or a custom inbound port (Standard SKU or higher required for custom ports).
User Permissions:
• The user must have access rights on the target VM. If not an admin, they should be added to the Remote Desktop Users group.
Azure Network Watcher: Monitoring and Troubleshooting
Azure Network Watcher provides tools to monitor, diagnose, and troubleshoot network issues for Azure IaaS resources like VMs, VNets, load balancers, and application gateways. It is not designed for PaaS monitoring or web analytics.
Key Features:
1. Monitoring:
• Topology: Visualizes the entire network, showing resource relationships.
• Connection Monitor: Tracks end-to-end network performance across Azure and hybrid environments.
2. Network Diagnostic Tools:
• IP Flow Verify: Identifies traffic filtering issues at the VM level.
• NSG Diagnostics: Checks security rules for traffic filtering at various levels.
• Next Hop: Analyzes routing paths for network traffic.
• Effective Security Rules: Shows security rules applied to a network interface.
• Connection Troubleshoot: Tests network connections between various endpoints.
• Packet Capture: Enables remote traffic capture for troubleshooting.
• VPN Troubleshoot: Diagnoses issues in virtual network gateways and connections.
3. Traffic Analysis:
• Flow Logs: Logs IP traffic through NSGs and VNets for analysis.
• Traffic Analytics: Provides insights and visualizations of network traffic data.
Automatic Enablement:
Network Watcher is automatically enabled when a virtual network is created or updated, with no added cost. If previously disabled, it must be manually enabled.
This toolset enhances network visibility, security, and performance in Azure environments.
Planning Storage for Azure Virtual Desktop User Data
Azure provides multiple storage solutions for FSLogix profile containers in Azure Virtual Desktop (AVD). FSLogix enables seamless profile roaming by attaching a Virtual Hard Disk (VHD/VHDX) at sign-in, making user profiles instantly available.
Comparison of Storage Solutions
| Feature | Azure Files (Recommended) | Azure NetApp Files | Storage Spaces Direct |
| Use Case | General purpose | Enterprise-scale | Cross-platform |
| Platform Service | Azure-native | Azure-native | Self-managed |
| Availability | All regions | Select regions | All regions |
| Redundancy | LRS/ZRS/GRS/GZRS | LRS/ZRS w/ replication | LRS/ZRS/GRS |
| Performance | Up to 100K IOPS, 10 GBps | Up to 460K IOPS, 4.5 GBps | HDD: 500 IOPS, SSD: Up to 20K IOPS |
| Capacity | 100 TiB/share, 5 PiB/account | 100 TiB/volume, 12.5 PiB/account | 32 TiB/disk |
| Infrastructure | Min. 1 GiB share | Min. 2 TiB pool, 100 GiB volume | Min. 2 VMs, Cloud Witness |
| Protocols | SMB 3.0/2.1, NFSv4.1, REST | NFSv3/4.1, SMB 3.x/2.x | NFSv3/4.1, SMB 3.1 |
Recommendation:
Azure Files is the best choice for most deployments due to its scalability, availability, and performance, making it ideal for FSLogix profile storage in Azure Virtual Desktop.
Azure Storage Management Summary:
Azure Files: Supports cloud, on-premises, and hybrid access (via Azure file sync). Backup uses Azure backup snapshot integration. Offers full security and compliance with all Azure-supported certificates. Integrates with Native Active Directory and Microsoft Entra Domain Services.
Azure NetApp Files: Available in cloud and on-premises. Uses NetApp snapshots for backup. Security with Azure-supported certificates. Integrates with Microsoft Entra Domain Services and Native Active Directory.
Storage Spaces Direct: Offers cloud and on-premises access. Backup uses Azure backup snapshot integration. Secured with all Azure-supported certificates. Integrates with Native Active Directory or Microsoft Entra Domain Services.
For pricing, refer to Azure Virtual Desktop plans.
Azure Files tiers
Azure Files offers two storage tiers: Premium and Standard, designed to balance performance and cost based on workload needs.
Premium file shares use SSDs, provide high performance, and are best for IO-intensive workloads. They are billed based on provisioned storage, not usage.
Standard file shares use HDDs, offer reliable performance for less demanding workloads, and are billed based on storage usage and transactions.
Workload Recommendations:
Light (fewer than 200 users): Standard
Light (more than 200 users): Premium or Standard with multiple shares
Medium & Heavy: Premium file shares
Implementing Storage Accounts for Azure Virtual Desktop
Azure storage accounts serve as top-level objects for shared storage, supporting multiple file shares. There are two main types of storage accounts for Azure Files:
General Purpose v2 (GPv2): Used for standard file shares on HDD-based hardware. It supports multiple storage resources like blobs, queues, and tables. File shares can be deployed in transaction-optimized, hot, or cool tiers.
FileStorage: Used for premium file shares on SSD-based hardware, supporting only Azure file shares with no other storage resources.
Creating a Storage Account:
In the Azure portal, go to + Create a resource, search for "storage account," and select it.
In the Basics section:
For GPv2: Set Performance to Standard and Account kind to StorageV2.
For FileStorage: Set Performance to Premium and Account kind to FileStorage.
Additional fields:
Storage account name: Must be globally unique (3-24 characters, lowercase letters and numbers).
Location: Choose a region for deployment.
Replication: Select redundancy options (LRS, ZRS, GRS, GZRS, RA-GRS, RA-GZRS).
Networking: Optional settings that can be configured later.
Data Protection: Configure the soft-delete policy for file shares. Other settings for blobs and containers are not applicable to file shares.
Create and configure host pools and session hosts for Azure Virtual Desktop
Prerequisites for Azure Virtual Desktop
To deploy Azure Virtual Desktop (AVD), you need:
1. Azure Subscription
An active Azure account with a valid subscription.
Appropriate Role-Based Access Control (RBAC) permissions (Contributor or Owner) to register the Microsoft.DesktopVirtualization resource provider.
2. Identity & Authentication
Microsoft Entra ID (formerly Azure AD) is required for user authentication.
Session hosts can be joined to:
Microsoft Entra ID
Active Directory Domain Services (AD DS)
Microsoft Entra Domain Services
If using hybrid identities, user accounts must be synchronized between AD DS and Microsoft Entra ID.
3. Session Hosts
Must be joined to the same identity provider as the users.
For Azure Stack HCI, session hosts must be joined to AD DS.
Proper permissions are needed to join session hosts to the directory.
4. User Accounts
Must exist in Microsoft Entra ID.
If using AD DS or Microsoft Entra Domain Services, accounts must be synchronized.
B2B, B2C, or personal Microsoft accounts are not supported.
5. FSLogix Profile Container (Optional)
Requires Azure Files or Azure NetApp Files for profile storage.
Hybrid identities are required for FSLogix when using Microsoft Entra ID.
6. Deployment Parameters
Domain name (if using AD DS or Microsoft Entra Domain Services).
Credentials to join session hosts to the domain.
MFA cannot be enabled on the domain join account.
For more details, refer to Supported Identities and Authentication Methods.
Azure Virtual Desktop: Supported Operating Systems & Regions
Supported Operating Systems
Azure Virtual Desktop supports 64-bit OS versions for session hosts, aligned with the Microsoft Lifecycle Policy:
| Operating System | Internal Commercial Licensing | External Commercial Licensing |
| Windows 11/10 Enterprise Multi-Session | Microsoft 365 E3/E5, A3/A5, F3, Business Premium, Education A3/A5, VDA | Per-user access pricing via Azure subscription |
| Windows Server 2022/2019/2016 | RDS CAL with Software Assurance (per-user/device) | Windows Server 2022 RDS SAL |
Unsupported Items:
32-bit OS, Windows N/KN/LTSC editions
Ultra disks & ephemeral OS disks
Virtual Machine Scale Sets
Windows 7 (support ended Jan 10, 2023)
Windows Server 2012 R2 (support ended Oct 10, 2023)
OS Deployment Methods
Azure Marketplace images
Custom images (Azure Compute Gallery, managed images)
Azure Stack HCI (Marketplace, Azure Storage, or local share)
VM Licensing & Activation
Internal users: No extra license needed if covered under Microsoft 365 or Windows Enterprise.
External users: Requires per-user access pricing with an Azure subscription.
Azure Stack HCI: Requires OS activation before use.
Azure Regions for Deployment
Metadata for host pools, workspaces, and app groups can be stored in:
Americas: Central US, East US, East US 2, North Central US, South Central US, West Central US, West US, West US 2, West US 3, Canada Central, Canada East
Europe: North Europe, West Europe, UK South, UK West
Asia-Pacific: Australia East, Central India, Japan East
Sovereign Clouds: Azure for US Government, Azure operated by 21Vianet (China)
For seamless operation, update Azure Stack HCI VMs with the latest cumulative security update before June 17, 2024.
Azure Virtual Desktop: Network & Remote Desktop Client Planning
Network Requirements
Users establish a secure reverse connection (no inbound ports needed).
TCP 443 is used by default; RDP Shortpath (UDP) can be used for better performance.
A virtual network and subnet must be in the same Azure region as session hosts.
Ensure connectivity to domain controllers and DNS servers for AD DS or Microsoft Entra Domain Services.
Allow TCP 443 traffic to required Azure Virtual Desktop URLs; unblock Microsoft 365 endpoints if needed.
Keep round-trip latency below 150ms for best performance.
Use Azure Firewall to enhance security and restrict outbound traffic.
Avoid opening port 3389; use just-in-time VM access for troubleshooting if necessary.
No public IPs should be assigned to session hosts.
Session Host Management
Windows Installer must be enabled to allow agent updates.
Intune Management:
Supported: AD DS with Microsoft Entra hybrid join.
Not supported: Microsoft Entra Domain Services or Windows Server session hosts.
Use Group Policy instead for Windows Server management.
Remote Desktop Clients
Azure Virtual Desktop supports the following clients:
Windows Desktop client
Azure Virtual Desktop Store app for Windows
Web client
macOS, iOS, iPadOS, Android, and Chrome OS clients
Remote Desktop app for Windows
⚠️ Not Supported: RemoteApp and Desktop Connections (RADC) or MSTSC client.
Creating a Host Pool in Azure Virtual Desktop
Azure Virtual Desktop licensing applies to Windows and Windows Server virtual machines (VMs) registered as session hosts. It does not cover VMs used as file share servers or domain controllers.
Ways to Apply a License
Azure Marketplace – Automatically applies the license when creating a host pool.
Azure Resource Manager (ARM) Template (GitHub) – Also applies the license automatically.
Manual Application – Apply a license to an existing session host VM.
Applying a Windows License to a Session Host VM
Run the following PowerShell commands:
$vm = Get-AzVM -ResourceGroup <resourceGroupName> -Name <vmName>
$vm.LicenseType = "Windows_Client"
Update-AzVM -ResourceGroupName <resourceGroupName> -VM $vm
Verifying the License on a Session Host VM
After deployment, check if the license is applied:
Get-AzVM -ResourceGroupName <resourceGroupName> -Name <vmName>
✅ Correctly Licensed VM Output:
Type : Microsoft.Compute/virtualMachines
Location : westus
LicenseType : Windows_Client
❌ VM Without a License:
Type : Microsoft.Compute/virtualMachines
Location : westus
LicenseType :
Listing All Licensed Session Host VMs
To find all session hosts with the Windows license applied in your Azure subscription:
$vms = Get-AzVM
$vms | Where-Object {$_.LicenseType -like "Windows_Client"} | Select-Object ResourceGroupNa
Creating a Host Pool Using Azure PowerShell
You can create a Pooled or Personal host pool using the Az.DesktopVirtualization PowerShell module.
Prerequisites
Azure Cloud Shell: Ensure the correct subscription context is set.
Local PowerShell: Sign in to Azure and set the appropriate subscription.
Creating a Pooled Host Pool
Uses Breadth-First load balancing and Desktop as the preferred app group type.
$parameters = @{
Name = '<Name>'
ResourceGroupName = '<ResourceGroupName>'
HostPoolType = 'Pooled'
LoadBalancerType = 'BreadthFirst'
PreferredAppGroupType = 'Desktop'
MaxSessionLimit = '<value>'
Location = '<AzureRegion>'
}
New-AzWvdHostPool @parameters
Creating a Personal Host Pool
Uses Persistent load balancing with Automatic assignment.
$parameters = @{
Name = '<Name>'
ResourceGroupName = '<ResourceGroupName>'
HostPoolType = 'Personal'
LoadBalancerType = 'Persistent'
PreferredAppGroupType = 'Desktop'
PersonalDesktopAssignmentType = 'Automatic'
Location = '<AzureRegion>'
}
New-AzWvdHostPool @parameters
Verify the Host Pool
Check the properties of your host pool:
Get-AzWvdHostPool -Name <Name> -ResourceGroupName <ResourceGroupName> | FL *
Adding Session Hosts to a Host Pool in Azure Virtual Desktop
To add session hosts, you first generate a registration key, then create and register session hosts.
1. Generate a Registration Key
A registration key is needed to authorize session hosts to join a host pool.
Steps to Generate a Key in the Azure Portal
Sign in to the Azure portal.
Search for Azure Virtual Desktop and select it.
Navigate to Host Pools and choose your target host pool.
In the overview, select Registration Key → Generate new key.
Set an expiration date/time and confirm with OK.
Copy or download the registration key for later use.
2. Create and Register Session Hosts
You can create session hosts and register them using the Azure Virtual Desktop service, ARM templates, or other automated methods.
Using the Azure Portal
Go to Azure Virtual Desktop → Host Pools → Select your host pool.
Click Session hosts → + Add.
Under Virtual Machines, configure the settings (Azure or Azure Stack HCI).
Add optional Tags, then proceed to Review + Create.
Click Create to complete the process.
✅ Session hosts will automatically appear in the host pool after deployment.
3. Register Manually Created Session Hosts
For session hosts created outside of Azure Virtual Desktop (e.g., automated pipelines), install and configure the necessary agents.
Steps to Register Manually Created Session Hosts
Ensure the VM is joined to Microsoft Entra ID or Active Directory.
If using Windows Server, install the Remote Desktop Session Host role and restart.
Download and install the required agents:
Install the Agents:
Run:
Microsoft.RDInfra.RDAgent.Installer-x64-<version>.msiPaste the registration key when prompted.
Run:
Microsoft.RDInfra.RDAgentBootLoader.Installer-x64.msi
After installation, session hosts will appear in the host pool (initially as Unavailable, but they will update automatically).
4. Licensing Considerations
Azure Virtual Desktop licenses are automatically applied when using the service.
For Windows Server session hosts, an RDS Client Access License (CAL) is required.
For Azure Stack HCI, activate Windows licenses before using them in AVD.
Customize Remote Desktop Protocol (RDP) Properties for a Host Pool
Customizing RDP properties enhances the user experience by adjusting settings like multi-monitor support and audio redirection. Use the -CustomRdpProperty parameter in the Set-RdsHostPool cmdlet to modify these settings.
Default RDP Properties
| RDP Property | Desktops | RemoteApps |
| Multi-monitor mode | Enabled | N/A |
| Drive Redirection | Drives, clipboard, printers, COM ports, USB devices, smartcards | Drives, clipboard, printers |
| Remote Audio Mode | Play locally | Play locally |
Modify Custom RDP Properties
1. Add/Edit a Single RDP Property
Set-RdsHostPool -TenantName <tenantname> -Name <hostpoolname> -CustomRdpProperty "<property>"
2. Add/Edit Multiple RDP Properties
$properties = "<property1>;<property2>;<property3>"
Set-RdsHostPool -TenantName <tenantname> -Name <hostpoolname> -CustomRdpProperty $properties
3. Reset All Custom RDP Properties
Set-RdsHostPool -TenantName <tenantname> -Name <hostpoolname> -CustomRdpProperty ""
This restores all RDP properties to their default values.